To be frank, a lot of cyber security presentations are, well… dull.
Slideshows are awful and tedious, reinforcing the “nerdy IT guy” image of security. And audience members don’t want to hear boring theoretical explanations of how cyber attacks work. Even broken in layman’s terms, these lessons are hard for someone without deep technical knowledge to understand— never mind to retain— without proper context.
Your team learns best by direct example, and nothing gets the message across quite like live hacks right before their eyes.
Yet surprisingly, not many cyber security speakers want to take on the pressure of executing a live hacking demonstration in front of a captive audience. It takes extensive planning and experience; if those hacks don’t pan out as promised, audiences are disappointed and everyone feels a little embarrassed. But the right talent can undeniably improve your security initiative and— yes! — excite your audience during cyber security events.
Once called the world’s most famous hacker, Kevin Mitnick is your man, and we’re here to explain why.
1. Engaging Storytelling
Some cyber security experts, unfortunately, fall into their own cliche: the nerdy code-crawler who is more comfortable behind the desk than in front of people. The result is an uncharismatic speaker nervously taking the virtual stage, delivering presentations and live hacks without much excitement. Without the right enthusiasm and narrative, it’s easy for a security presentation to be boring and for guests to become unengaged.
THE MITNICK DIFFERENCE: “Boring” isn’t a word you’d ever use to describe Kevin Mitnick. He’s known within the industry for his charm and exceptional storytelling, during live hacks especially, detailing the full narrative in a way that makes listeners feel involved and entertained. Watchers see the full picture, from the idea that inspired the attack throughout its actual execution, to understand the full scope of the breach.
2. Adaptability to Change
The COVID-19 pandemic brought with it big changes in the world of event planning. Cyber security speakers who were used to appearing on stage were now forced to pivot their presentations to virtual cyber security events— and some didn’t have the easiest transition.
Although cyber security speakers are considered tech savvy, many struggled to connect via virtual media and keep watchers engaged over the screen. From glitchy WiFi issues to low-quality streams, some speakers charge top dollar for virtual broadcasts that under deliver, leaving sponsoring organizations feeling like their investments were ill-made.
THE MITNICK DIFFERENCE: A year ago, Kevin Mitnick decided to double down on online engagements to transition smoothly into the virtual world. We invested in some of the best tech in the business for virtual events and webinars— like professional cameras, lighting and audio— to ensure a clear broadcast, every time. We also took the time to really get comfortable with our online event platforms, and to ensure our event hosts were also up to par. The result? Webinars and online cyber security workshops that are just as impressive (if not more convenient) than in-person events.
3. Fresh Content
Bad actors are constantly discovering new vulnerabilities— almost daily— and it can be a full-time job keeping up with the ever-growing threat landscape. Cyber security pros keep up with all of these changes, but many speakers spend weeks putting together robust keynotes...and once that presentation is approved, they rehash that same speech for months or even years to come. Examples quickly become dated and emerging cyber threats and hacking techniques are never addressed.
What kind of emerging threats can a great speaker deliver to your audience? A prime example of this is the 2020 USB Ninja Cable, a seemingly “normal” USB cord that bad actors are now plugging into unsuspecting victims’ computers to steal data. This is just one example: plenty of breaches occurred already in 2021, all of which denote powerful lessons cyber security presenters should be using in their educational content.
THE MITNICK DIFFERENCE: Our team works day-in-and-day-out to keep up with ever-evolving cyber threats. We keep our community informed on the new tricks bad actors hide up their sleeves— and we take it a step further by weaving these important narratives into our live hacking demonstrations. You’ll never find a presentation that’s irrelevant in the field, and Kevin loves using his incredible storytelling skills to paint real lessons from real breaches.
4. A Variety of Threat Demonstrations
Some cyber security keystone speakers not only rehash outdated content, they also limit their presentations to a small number of topics. If a speaker only delivers two or three presentations, year after year, you’ll quickly find yourself on the hunt again for another presenter.
Working with a speaker who has a breadth of knowledge in cybersecurity and a generous list of presentations means your company can choose exactly what fits your needs. Leading speakers should also customize the presentation for your audience’s knowledge, experience and skills. In our field, this can be hard to find!
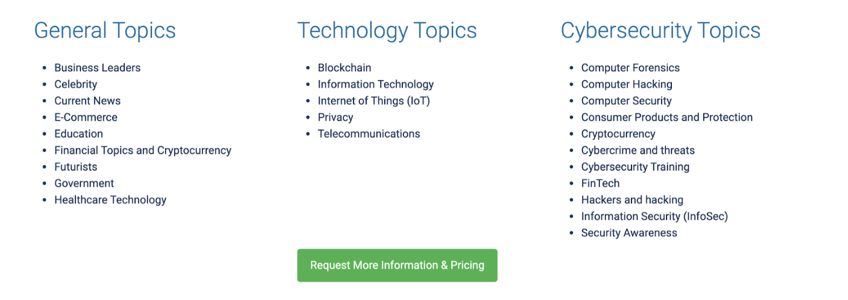
THE MITNICK DIFFERENCE: At Mitnick Security, we don’t like limiting our presentations. While we absolutely prioritize quality over quantity, we’re proud to say we have a deep network of skills and expertise to talk about a wide range of topics, from business or technology to information security. Explore some of our popular keynotes here, but remember, we are also open to personalizing an experience exclusively for your company.
5. Interactivity
Many virtual events in cyber security are pre-recorded scripted shows. Guests join webinars only to watch an emcee hit play and show a reel of the “live hack” or security presentation. While there’s nothing wrong with preparing content ahead of time, presentations like these leave no room for audience participation. Virtual cyber security event attendees are in no way obligated to pay attention and get involved in learning— and oftentimes do other things while the presentation plays in the background.
THE MITNICK DIFFERENCE: While our team does use pre-recorded content, we still believe in the power of a true live hacking experience. That’s why we do offer demonstrations in this fashion, for a real live-streamed webinar. We also incorporate live Q&A sessions at the end of the presentation, giving attendees a chance to ask important questions and participate in the digital broadcast— instead of sitting muted behind the screen the whole time.
Choose a Cyber Security Speaker with Confidence
If you’re trying to decide on the right security speaker for your next virtual event, we have a handy resource for you. In Choosing the Right Cyber Security Keynote Speaker, you’ll find a few important, uncompromisable characteristics to look for in your next big presenter.
Interested in booking Kevin Mitnick, specifically? Explore our virtual event topics here.