Most companies tell their employees to be on the lookout for email scams, yet not all take the time to educate their team on what these malicious messages look like.
There’s a misconception that scam emails are mass-sent messages, wherein hackers cast a wide net and disperse impersonal messages to hundreds or thousands of recipients. While those emails do exist, most social engineers or threat actors don’t do that at all. When “phishing” for a target, professional social engineers focus on one individual guppie, not the whole pond. They spear phish.
The proof is in the data. “A whopping 91% of cyberattacks and the resulting data breach begin with a spear phishing email,” according to research from security software firm Trend Micro.
Because an overwhelming majority of cyber attacks start with a well-orchestrated phish, it’s pertinent to become familiar with this common hacking technique.
What is Spear Phishing, Exactly?
Imagine someone fishing. What tools do they have? You’re probably imagining a rod and a net, and if you’re thinking old school, maybe a spear. When fishing for...fish, you can try to scoop up many little fish with your net, or get more targeted and go after a bigger fish with your rod and really good bait.
Similarly, Phishers who send spam emails have two options. KnowBe4 calls the first wide-net approach the “spray and pray” technique: it’s a “get as many email addresses from the organization they can, and send them all an email that they might click on” approach.
The second tactic is referred to as “spear phishing,” where the attacker targets individuals. Just like in a pond where an angler would focus on one location to ensure they’re hooking the best possible fish, social engineering phishers choose their email target, trick the person into thinking they’re a friendly or unthreatening source, and then deliver them a hard blow when they least expect it!
A spear phishing attack is one in which a social engineer uses deep knowledge of the potential victim to trick them into taking an action that’ll gain them access to private data.
How Hackers Hunt their Target
Now that you know that spear phishers go after individuals, it’s helpful to understand why the hacking technique is so successful.
Social engineers begin by finding a company they’re interested in targeting for various reasons: the value of the data they hold, their security gaps, their customer information... They then scour the Internet for publicly accessible, open-source data on the business (called open-source intelligence or OSINT) using various free tools and public profiles like a business’ Facebook, LinkedIn, etc. From there, the bad actors often research individual employees and managers, compiling information about them using the same tools and social media outlets mentioned above.
The social engineers then use this OSINT to weave a convincing story or narrative in an email to trick their targets. Perhaps the bad actor pretends to be from the same high school as their prey, “Go Wild Cats!,” or claim they know a fellow employee, “Tom and I go way back!” The hacker uses a trustworthy-looking email address to build a false connection or relationship.
After a few foundational emails to build a rapport, the bad actor usually sends a malware-injected link or asks the target to perform an action for them, like opening an attachment, which infects their device with malicious software.
Spear Phishing Email Examples
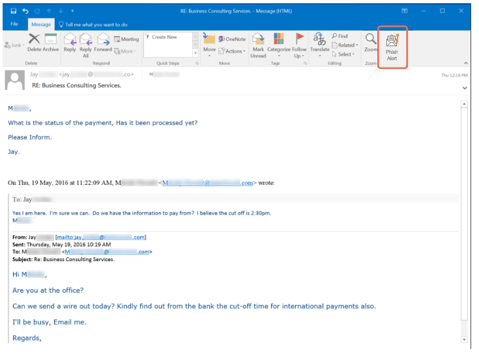
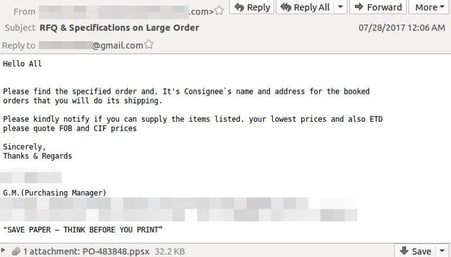
The following examples are from the team at KnowBe4. Note that they look very much like real emails, but are actually targeted, fraudulent communications.
. 
COVID-19 Phishing Email Scams
Spear phishing emails take many different forms, but a common theme in 2020 has been COVID-19 related scams. Here are just two examples:
- Direct deposit email scams. A malicious email may ask to send you a direct deposit in light of a new stimulus bill. They could mimic the look of a government site and ask you to enter your banking routing number to receive a direct deposit of your payout.
- Hospital email scams. A bad actor could imitate a hospital, warning you that rooms are filling up fast and that it may be wise to pre-register in the event a loved one falls ill.
Read more examples of COVID phishing emails here.
Watch out for Whaling Attacks Too
Sometimes instead of targeting employees, phishers will go after the “big fish.” Whaling is a term used for social engineers who invest in researching and targeting higher-tiered employees and management who boast higher permissions and can grant bad actors deep access to internal databases.
It’s pertinent to educate your senior management on the dangers of whaling scams and ensure they recognize that they’re not impervious to phishing scams. Learn more about whaling here.
It’s Not Just Spear Phishing You Have to Worry About
Spear phishing is just one way bad actors pose clever social engineering attempts on unsuspecting employees and management. Read more about the top hacking techniques all CISOs should know about here.
The Power of Social Engineering Training
There’s no sure way to filter out and block all scam emails. Because of this, educating your team on the threat landscape is really the best prevention for a social engineering hack.
Invest in social engineering training to teach your team exactly what to lookout for, including how to recognize a suspicious email, how to best report any odd messages to management, and more.
Curious to see how your team would stand up against phishing attacks without any formal training? Invest in social engineering strength testing with some of the best in the industry, Kevin Mitnick and his Global Ghost Team.




